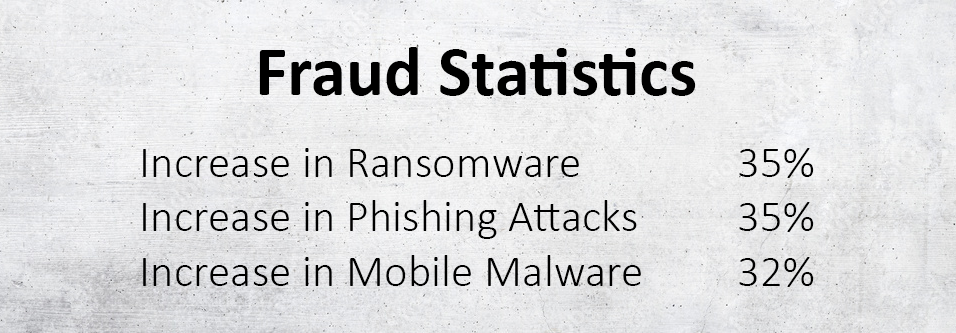
Cyber-attacks are increasing year over year. With most of us working remotely on a consistent basis (26% of the American workforce to be exact), cyber-attacks have increased in a similar fashion. So, what can we do internally to take preventative measures? What are cyber attacks and how are they implemented? This month’s issue will discuss common fraud to look out for and steps you can take right now to protect yourself and possibly your credit union’s private information.
What is a Cyber Attack?
Any attempt to steal, expose, alter, disable, or destroy information through unauthorized access to computer systems is considered a cyber-attack
Virus: A dangerous program designed to replicate and install itself to multiple hidden areas in your computer. Viruses can change vital code in your computer to prevent normal operation.

Spyware: A program designed to spy on a user and their activity such as browsing history, keystrokes, or any number of actions that are implemented on your device.

Spyware: A program designed to spy on a user and their activity such as browsing history, keystrokes, or any number of actions that are implemented on your device.

Worms: A malicious program focused on infecting a network to download files, replicate itself to slow down a system, and/or create weak spots in security for a criminal to access

Phishing: A technique for attempting to acquire sensitive data, such as bank account numbers, through fraudulent solicitation in email or on a web site, in which the perpetrator masquerades as a legitimate business or reputable person.
You will notice that most of these examples of malicious software have a different tactic to get into your computer or network, but all of them try to accomplish the same feats once the user accidentally or mistakenly installs them. The important take away from these examples is to NEVER type your username, passwords, personal information, into a device or application without knowing 100% that it is a trusted source. The spam emails responsible for most of these can be detected through virus scanning and security software, but a major red flag you should look out for is the email address that sent the link. For example, If the spam email was in fact from Facebook, then the email address would end in @facebook.com. Don’t click on email links that claim to be from reputable sources. Instead, lookup the company yourself and contact them through their normal channels to see if the email is legitimate.
How Can You Protect Yourself from Cyber Attacks?
It’s important to be aware of what antivirus protection software can do and which ones are top rated. We have put together a list of the top-rated FREE antivirus protection programs available today. Most of these programs come with a minimal protection at no cost to you, but they also have available payment upgrades that could be an added benefit.
The following Information was provided by PC Magazine (pcmag.com). Car Solutions is in no way affiliated with PC Magazine. We are simply providing information we found useful to this subject.
AVAST: 4.5/5.0 RATING
PROS:
- Excellent antivirus Lab Scores
- Very good scores in hands-on testing
- Protection for Windows, macOS, Android, and iOS
- Generous VPN bandwidth limit
- Includes privacy and performance features
CONS:
- Protection limited on Android, more so on iOS
- Advanced firewall features not applicable
- No Wi-Fi Inspector
- Many useful features require upgrade.
KASPERSKY: 4.5/5.0 RATING
PROS:
- Perfect or near-perfect scores from four independent testing labs
- Effective ransomware protection
- Very good score in phishing protection test
- Good scores in malware-blocking test
- Support for Android and iOS
- Free
CONS:
- No direct tech support
- Features for iOS is limited
AVG: 4.0/5.0 RATING
PROS:
- Excellent scores from labs
- Very good scores in hands-on testing
- Boot-time scan removes persistent malware
- Some useful bonus features
- Free
CONS:
- Initial scan slower than average
- Fixing found performance issues requires upgrade
- Boot-time scan can be very slow
Ideas for Creating New Passwords
Instead of using common themes that can be discovered with a simple social media search like birthdays or anniversaries. You should try thinking of a sentence. For example, “The itsy bitsy spider went up the water spout.” Easy to remember by simply using the first letter of each word as your password (TIBSWUTWS). You could go even further to add lowercase/uppercase combinations (as well as a familiar date) and not even the NSA would be able to figure it out without help.
Does your credit union require frequent password changes? Continue the method above and just use the second verse. Write a hint on your notepad “Second verse” to remember which section of the nursery rhyme you are using this month.
